Effortlessly create a scalable Docker image factory in minutes with EC2 Image Builder
Containers based architectures are growing years after years, modernizing software delivery pipelines and and empowering his adopters to scale fast.
Far away from this promise, the reality is different: many companies are still struggling to create a proper build workflow for their Docker images, and the rise of vulnerabilities impacting containers increase the need of an efficient delivery pipeline to quickly answer this security issues.
Introduce late 2019 by AWS, EC2 Image Builder is a service originally designed to answer customers needs to about managing EC2 AMI, which are basically Docker images but for virtual machines rather than containers.
Paradigm
EC2 AMI and Docker Images are basically pretty similar talking about how it is build:
- For a EC2 AMIs, an EC2 instance is started, then custom operations are run into, such as updating the system or installing software. Instance is then stopped, and save as a template, called "AMI" (Amazon Master Image).
- For a Docker image, a container is a started, then custom operations are run into, such as updating the system or installing software. Container is then stopped, and save as a template, called "image".
Key features

Build components
Build components are scripts used in software development that outline a series of actions for downloading, installing, and setting up software packages, along with defining steps for validation.
Here's some examples of components:
aws-cli-version-2-linux: Installs the latest version of the AWS CLI version 2,update-linux-kernel-5: Installs the Linux kernel 5.* for Amazon Linux 2 from Amazon Linux Extras.
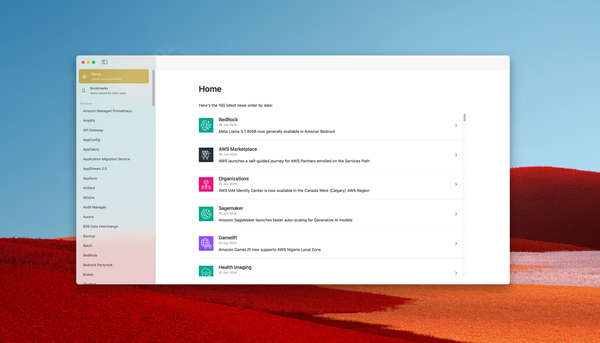
Recipes
A recipe is a document where components are used to create the target image.
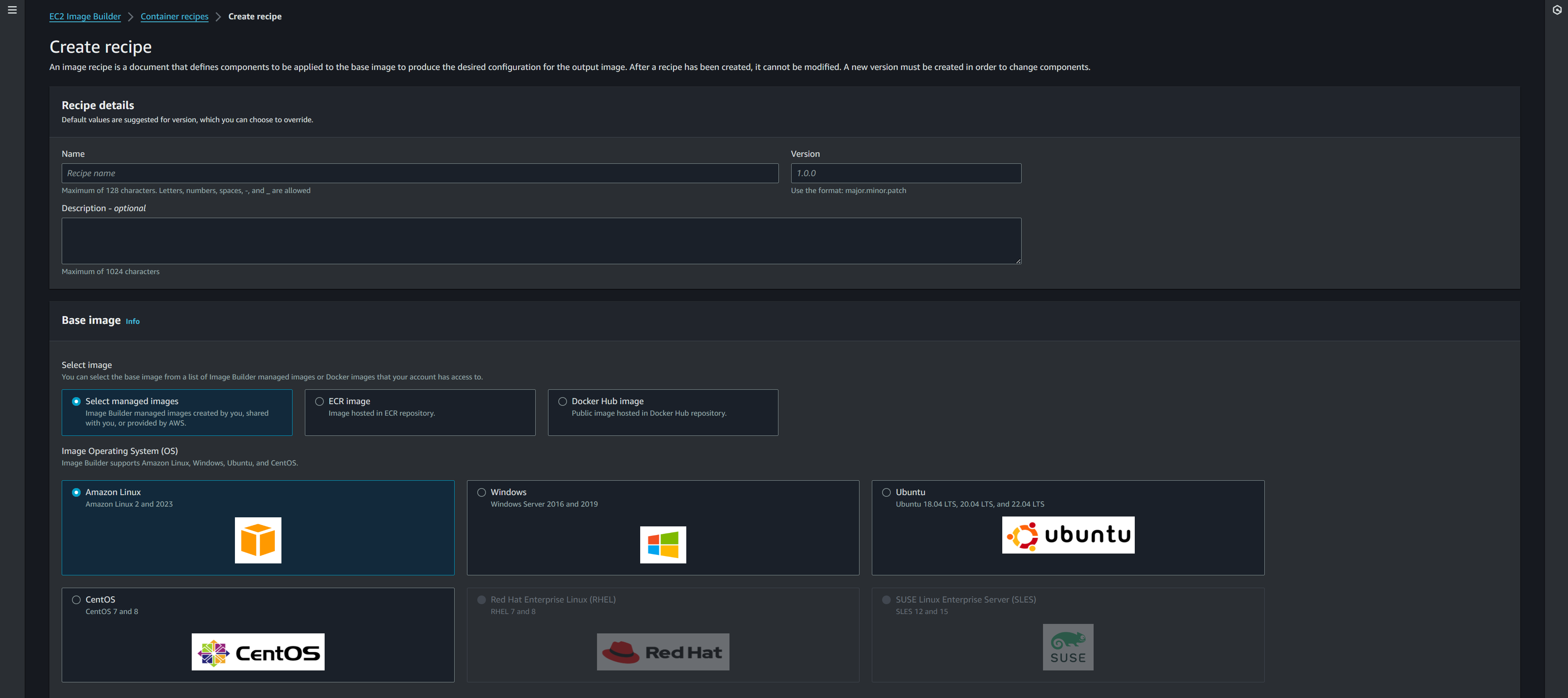
Multiples runtime are supported, from Windows to Linux. You can also use DockerHub or ECR Public as a source.
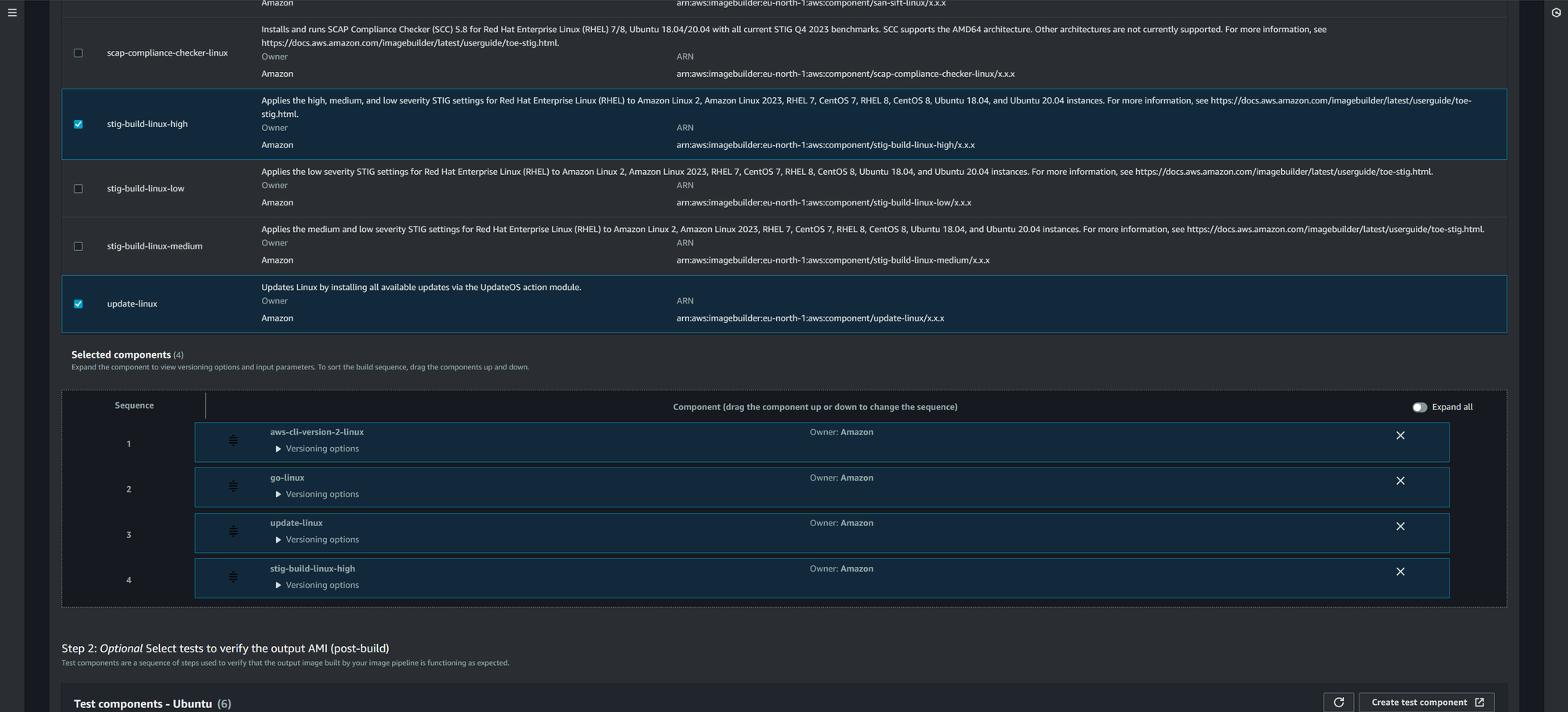
On this recipe, an Ubuntu 22 image is used as source from ECR Public Repository. 4 components are added in a specific order. Once image is build, EC2 Image Builder also offer to test it using custom or predefined rules:
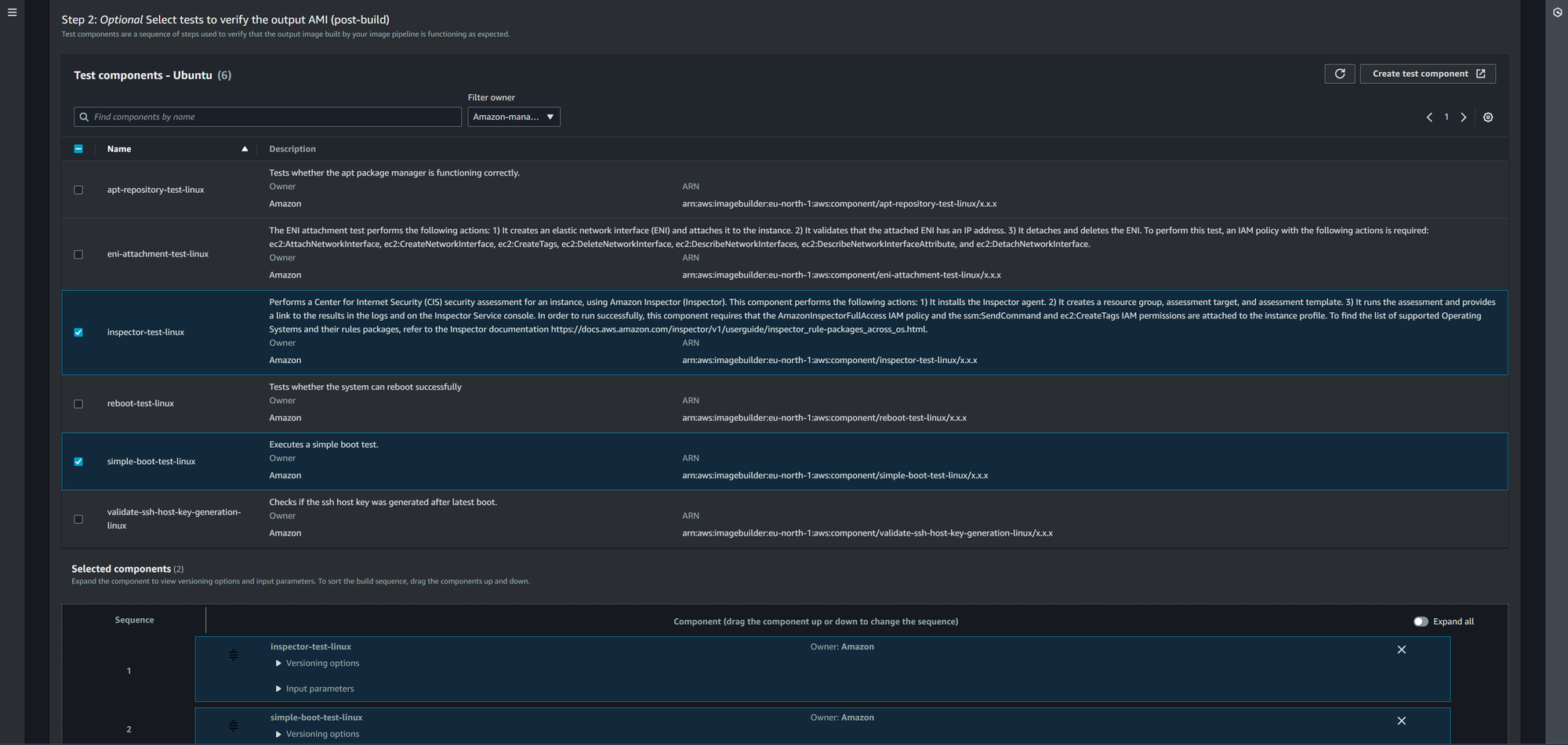
As EC2 Imager Builder is fully integrated with AWS ecosystem, you can use AWS Inspector to scan your image and assess his security level, to prevent publishing it if it does not fit your security constraints.
Lifecycles
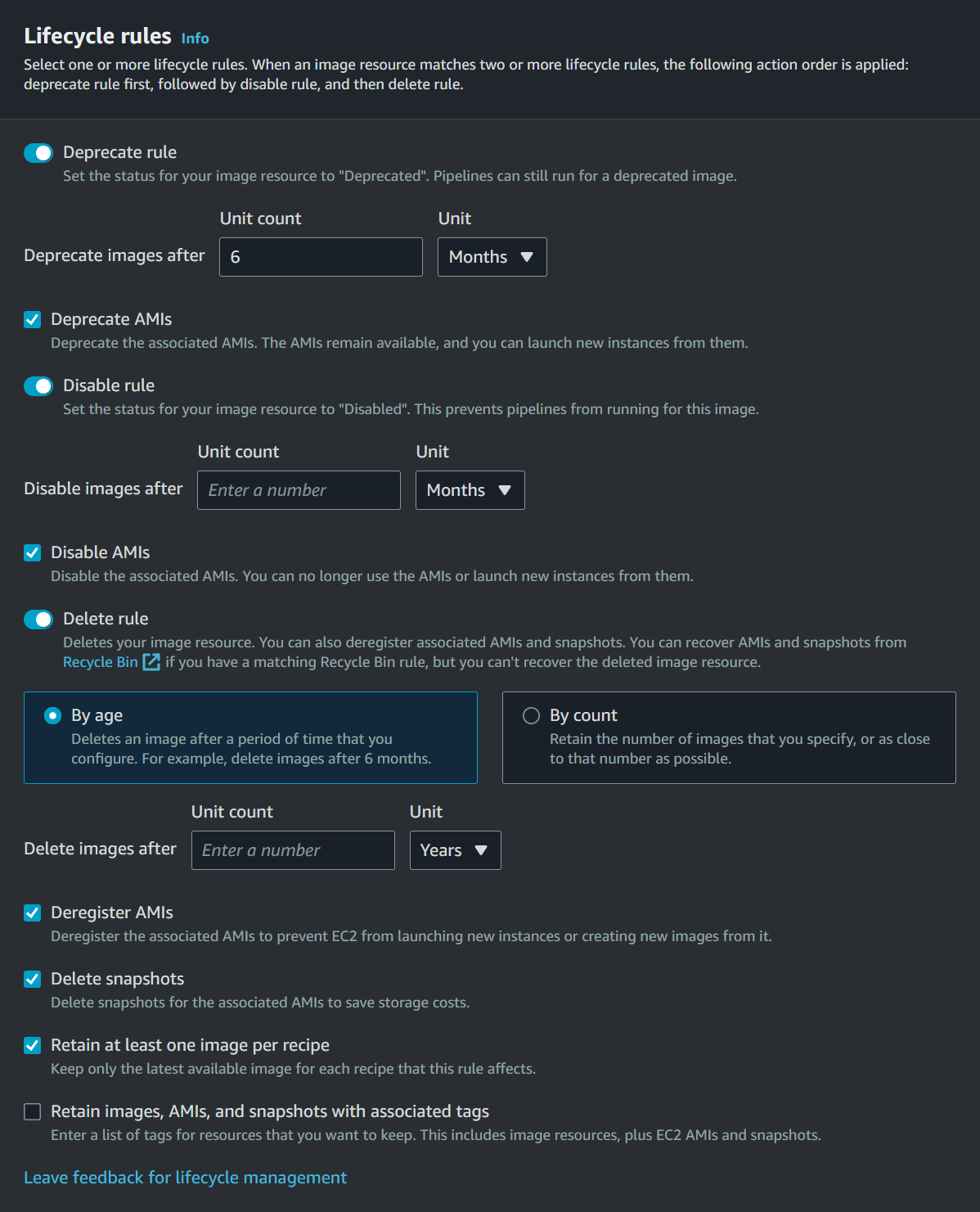
Lifecycle policies can be created via EC2 Image Builder to automate the management process of Docker Images or AMIs.
You can target a specific recipe or use tags to target multiples. Three rules are offered:
- Depreciation: image is flagged as deprecated but still can be used.
- Disable: Image is disabled, preventing pipelines to use it
- Deletion: Image is deleted
Pricing
Amazon EC2 Image Builder is offered at no cost, other than the cost of the underlying AWS resources used to create, store, and share the images